Description
Botnet focused mainly on DDOS attacks (TCP (SYN) Flood, UDP Flood, HTTP Flood)
Source code.
Infection Methods
Radware suspects the bot spreads via traditional means of infection such as exploit kits, spear phishing and spam emails.
Capabilities
Perform DDoS Attack:
The malware is capable of performing DDoS attacks using several vectors:
DNS Amplification
TCP (SYN) Flood
UDP Flood
HTTP Flood
Downloader:
The malware is capable of downloading malicious files from a remote server and executing the downloaded files on the infected machine. After looking at the downloaded files from several different botnets, Radware noticed cryptocurrency-related activity where some of the files are simple Monero cryptocurrency miners and others are the latest version of the “1ms0rry” malware associated with downloading miners and cryptocurrencies.
Proxy
The malware can turn the infected machine to a SOCKS/HTTP proxy to route traffic through the infected machine to a remote server.
Malware Behavior
The malware has a quick and silent installation with almost no changes on the infected machine. To ensure persistence on the infected machine it will either create a new key under the registry path “RunOnce” or create a new service on the system:
HKCU\Software\Microsoft\Windows\CurrentVersion\RunOnce\Registry Driver
HKLM\System\CurrentControlSet\Services\Icon Codec Service\
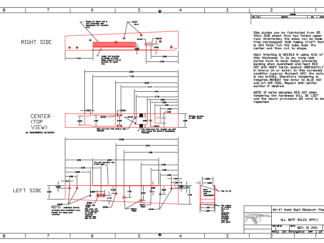
Communication
When the malware executes, it will generate an HTTP GET request to “/activation.php?key=” with a unique User-Agent string “2zAz.” The server will then respond with a “Fake 404 Not Found” message if there are no commands to execute on the infected machine.
Communication Obfuscation Example
The GET request param value is base64 encrypted.
The final readable string contains infected machine information as well as user information. When a new command is sent from the server “200 OK,” a response return is executed with the request to download a file from the server or execute a DDoS attack









Reviews
There are no reviews yet.